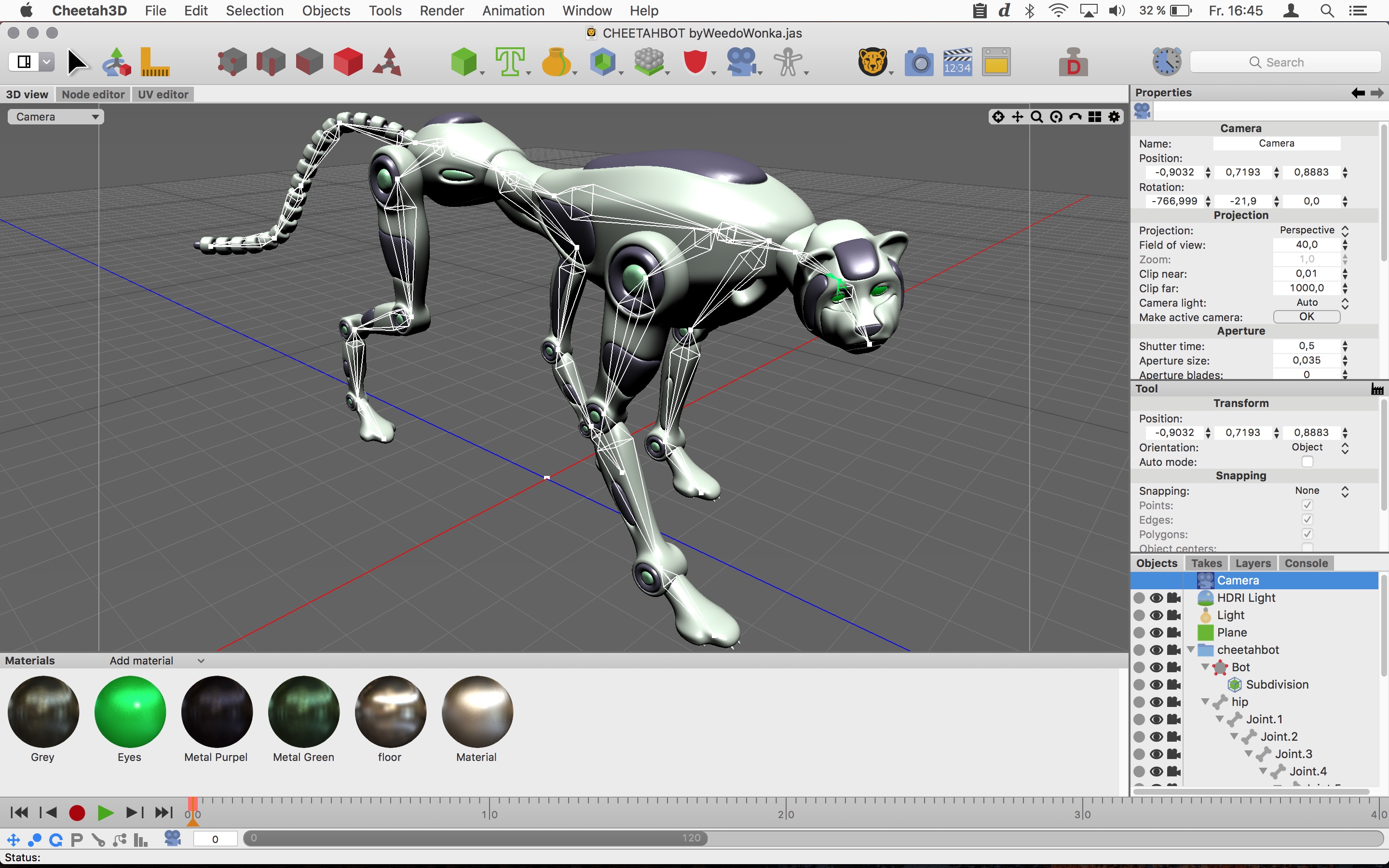
Images and animations made in Cheetah3D can also be shared using a wide range of popular image and movie file types (jpg, tiff, png, mov etc.). Workflow Cheetah3D integrates perfectly into the workflow of many popular Mac apps. With Cheetah3D you can create stunning 3D models for iBooks Author or many popular game engines. Cheetah3d free download - Cheetah3D, SketchUp Make 2017, Google Earth, and many more programs.
Cheetah3D on BBC iPlayer →
Cheetah3D creator Martin Wengenmayer appeared on the Cheetah3D forum recently and listed some of the features that we can expect to see in the upcoming Cheetah3D Version 7. Whilst there’s no release date yet, the new feature list does sound impressive… Adobe cs3 camera raw.
- New renderer
- NGon booleans
- Movie textures
- Soft selections
- Collada import
- Layers
- Big UI update
- and much much more
There’s a few in there that I’m pretty excited about, and I must confess I do know of some other features that are planned too but I’m sworn to secrecy on them!
New Renderer

My knowledge of rendering isn’t the best and I’m not sure what to expect here. Could we finally see the much requested render preview?
NGon Booleans
This is a big one. Booleans have never been particularly useful in Cheetah3D as the meshes that you end up with are quite messy. It’s very hard to move on and continue modelling after you’ve used a boolean at present. All this is set to change though. I can actually see this changing the way I model completely.
Movie Textures
Personally I’ve never really needed movie textures. I think this is because I largely produce still images with Cheetah3D. I can see a huge benefit here though and it’s something I’ve seen requested in the forum a good few times over the years. The possibilities here seem pretty endless. Initially I was just thinking about things like TV screens, but actually it could go way further than this.
Soft Selections
Soft selections is something I’ve personally requested. I first encountered them in Silo and what a great feature it is. If you’ve never used it, it’s quite hard to explain but I’ll try anyway:- Soft selection allows you to select part of a model and then take an additional softer selection of it’s surrounding points. The softer selection has less influence but whatever you do (move, scale) still has an impact. It’s an absolute must if you’re doing any organic modelling.
Layers
Probably the most intriguing feature on the list. I’ve not seen layers in any 3D application before. I’m not saying they don’t exist but it’s not something that I’ve used and I struggle to even understand how it would work. I’ve seen rendering to layers before in Strata but I don’t think this is what Martin is talking about. If anyone can enlighten me, I’d really appreciate it!
UI Update
A UI update is a scary thing for me! Does it mean that my tutorial that are all done in v5 and 6 will need updating? I have no idea at this stage.
That’s my thoughts. I’ve not mentioned the Collada import as I have no idea what Collada is really used for. Again I’m all ears if anyone wants to tell me!
For the protection of our customers, Apple does not disclose, discuss, or confirm security issues until a full investigation has occurred and any necessary patches or releases are available. To learn more about Apple Product Security, see the Apple Product Security website.
For information about the Apple Product Security PGP Key, see How to use the Apple Product Security PGP Key.
Where possible, CVE IDs are used to reference the vulnerabilities for further information.
To learn about other Security Updates, see Apple Security Updates.
Apple TV 7.0.3
Apple TV
Available for: Apple TV 3rd generation and later
Impact: A maliciously crafted afc command may allow access to protected parts of the filesystem
Description: A vulnerability existed in the symbolic linking mechanism of afc. This issue was addressed by adding additional path checks.
CVE-ID
CVE-2014-4480 : TaiG Jailbreak Team
Apple TV
Available for: Apple TV 3rd generation and later
Impact: Opening a maliciously crafted PDF file may lead to an unexpected application termination or arbitrary code execution
Description: An integer overflow existed in the handling of PDF files. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2014-4481 : Felipe Andres Manzano of the Binamuse VRT, via the iSIGHT Partners GVP Program
Apple TV
Available for: Apple TV 3rd generation and later
Impact: A local user may be able to execute unsigned code
Description: A state management issue existed in the handling of Mach-O executable files with overlapping segments. This issue was addressed through improved validation of segment sizes
CVE-ID
CVE-2014-4455 : TaiG Jailbreak Team
Apple TV
Available for: Apple TV 3rd generation and later
Impact: Opening a maliciously crafted PDF file may lead to an unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the handling of font files. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2014-4483 : Apple
Apple TV
Available for: Apple TV 3rd generation and later
Impact: Processing a maliciously crafted .dfont file may lead to an unexpected application termination or arbitrary code execution
Description: A memory corruption issue existed in the handling of .dfont files. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2014-4484 : Gaurav Baruah working with HP's Zero Day Initiative
Apple TV
Available for: Apple TV 3rd generation and later
Impact: Viewing a maliciously crafted XML file may lead to an unexpected application termination or arbitrary code execution
Description: A buffer overflow existed in the XML parser. This issue was addressed through improved bounds checking.
CVE-ID
CVE-2014-4485 : Apple
Apple TV
Available for: Apple TV 3rd generation and later
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: A null pointer dereference existed in IOAcceleratorFamily's handling of resource lists. This issue was addressed by removing unneeded code.
CVE-ID
CVE-2014-4486 : Ian Beer of Google Project Zero
Apple TV
Available for: Apple TV 3rd generation and later
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: A buffer overflow existed in IOHIDFamily. This issue was addressed through improved size validation.
CVE-ID
CVE-2014-4487 : TaiG Jailbreak Team
Apple TV
Available for: Apple TV 3rd generation and later
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: A validation issue existed in IOHIDFamily's handling of resource queue metadata. This issue was addressed through improved validation of metadata.
CVE-ID
CVE-2014-4488 : Apple
Apple TV
Available for: Apple TV 3rd generation and later
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: A null pointer dereference existed in IOHIDFamily's handling of event queues. This issue was addressed through improved validation.
CVE-ID
CVE-2014-4489 : @beist
Apple TV
Available for: Apple TV 3rd generation and later
Impact: Maliciously crafted or compromised iOS applications may be able to determine addresses in the kernel
Description: An information disclosure issue existed in the handling of APIs related to kernel extensions. Responses containing an OSBundleMachOHeaders key may have included kernel addresses, which may aid in bypassing address space layout randomization protection. This issue was addressed by unsliding the addresses before returning them.
CVE-ID
CVE-2014-4491 : @PanguTeam, Stefan Esser
Cheetah3d 7 3 3 0 Download 2020
Apple TV
Available for: Apple TV 3rd generation and later
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: An issue existed in the kernel shared memory subsystem that allowed an attacker to write to memory that was intended to be read-only. This issue was addressed with stricter checking of shared memory permissions.
CVE-ID
CVE-2014-4495 : Ian Beer of Google Project Zero
Cheetah3d 7 3 3 0 3
Apple TV
Available for: Apple TV 3rd generation and later
Impact: Maliciously crafted or compromised iOS applications may be able to determine addresses in the kernel
Description: The mach_port_kobject kernel interface leaked kernel addresses and heap permutation value, which may aid in bypassing address space layout randomization protection. This was addressed by disabling the mach_port_kobject interface in production configurations.
CVE-ID
CVE-2014-4496 : TaiG Jailbreak Team
Cheetah3d 7 3 3 0 6
Apple TV
Available for: Apple TV 3rd generation and later
Impact: A malicious, sandboxed app can compromise the networkd daemon
Description: Multiple type confusion issues existed in networkd's handling of interprocess communication. By sending a maliciously formatted message to networkd, it could be possible to execute arbitrary code as the networkd process. The issue is addressed through additional type checking.
CVE-ID
CVE-2014-4492 : Ian Beer of Google Project Zero
Apple TV
Available for: Apple TV 3rd generation and later
Impact: Style sheets are loaded cross-origin which may allow for data exfiltration
Description: An SVG loaded in an img element could load a CSS file cross-origin. This issue was addressed through enhanced blocking of external CSS references in SVGs.
CVE-ID
CVE-2014-4465 : Rennie deGraaf of iSEC Partners
Apple TV
Available for: Apple TV 3rd generation and later
Impact: Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution
Description: Multiple memory corruption issues existed in WebKit. https://sexsoft.mystrikingly.com/blog/notepad-direct-download. These issues were addressed through improved memory handling.
CVE-ID
CVE-2014-3192 : cloudfuzzer
CVE-2014-4459
CVE-2014-4466 : Apple
CVE-2014-4468 : Apple
CVE-2014-4469 : Apple
CVE-2014-4470 : Apple
CVE-2014-4471 : Apple
CVE-2014-4472 : Apple
CVE-2014-4473 : Apple
CVE-2014-4474 : Apple
CVE-2014-4475 : Apple
CVE-2014-4476 : Apple
CVE-2014-4477 : lokihardt@ASRT working with HP's Zero Day Initiative
CVE-2014-4479 : Apple
Apple TV
Available for: iPhone 4s and later, iPod touch (5th generation) and later, iPad 2 and later
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: The Kerberos libgssapi library returned a context token with a dangling pointer. This issue was addressed by improving state management.
CVE-ID
CVE-2014-5352